top of page

Gold Comet Blog
Search

Secure Collaboration for Regulated Industries: How to Protect Data Across Hybrid Teams
Secure collaboration has become one of the biggest cybersecurity challenges for regulated industries. Whether in defense, healthcare, finance, or government contracting, teams must work across hybrid environments, sharing sensitive data between internal employees, external partners, auditors, and customers.

Gold Comet
Feb 123 min read


Understanding GRC: Governance, Risk, and Compliance in the Defense Industrial Base
Many DIB organizations are adopting a GRC framework, Governance, Risk, and Compliance, to manage security responsibilities more effectively.

Gold Comet
Feb 42 min read


Secure Data Storage vs. “Compliant” Storage: What’s the Difference?
At Gold Comet, we believe secure data storage is about how data behaves after it is stored. Our platform ensures that every file, message, and record remains protected throughout its lifecycle—not just while sitting on a server.

Gold Comet
Jan 143 min read


Why Compliance Platforms Fail Without Secure Data Storage and Sharing Foundations
Searches for secure data storage and sharing foundations, and compliance platforms and data security for regulatory compliance are rising for a reason: organizations are recognizing that compliance starts with data protection, not just documented policies and striving to follow rules.

Gold Comet
Jan 72 min read


Why Strong Data Management and Backups Are Essential to Cybersecurity
In cybersecurity, prevention gets most of the attention, but data management and reliable backups determine whether an organization survives an incident or becomes a headline. Ransomware, insider mistakes, hardware failures, and cloud misconfigurations all have one thing in common: when data is lost or corrupted, recovery depends entirely on how well it was managed and backed up beforehand.

Gold Comet
Dec 17, 20253 min read

Why Privileged Access Management (PAM) Is Essential—And How Gold Comet Delivers It in Virginia
Privileged Access Management (PAM) has become a central pillar in modern cybersecurity frameworks, from CMMC to NIST 800-171 to enterprise-level governance programs. For organizations seeking a platform that’s built with PAM principles at its core, Gold Comet, our cybersecurity company based in Virginia, stands out as a secure, zero-trust, encryption-first alternative to legacy systems.

Gold Comet
Dec 10, 20254 min read


Data Security Posture Management (DSPM)
Compliance with security requirements is now more important than ever -- that means you should have a well implemented Data Security Posture Management Plan in place and operational! For those working in the DIB, CMMC accreditation has been made a federal requirement for the proposal bid process, contract and task order management, and participation in the federal supply chain. Here are some best practices to consider and what's on the horizon for DSPM.

Gold Comet
Nov 26, 20251 min read


The Next Wave of Cybercrime: Deepfakes, AI-Generated Ransomware, and Synthetic Identities
The cybercrime landscape is evolving faster than ever. Traditional threats like phishing and brute-force attacks remain prevalent, but there’s a new wave of attacks powered by artificial intelligence, deepfakes, and synthetic identities emerging.

Gold Comet
Oct 23, 20254 min read


Secure Data Sharing: How to Securely Share Sensitive Data in the US
Whether you’re exchanging medical records, government files, or corporate IP, secure data sharing solutions for businesses operating in the US are critical for avoiding breaches and data loss, fines, and brand damage.

Gold Comet
Oct 1, 20252 min read


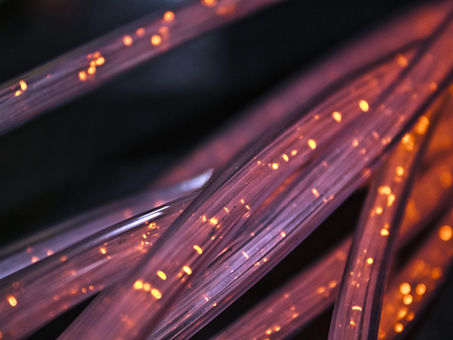
Where to Find Quantum-Secure Data Storage Services in Alexandria VA
Quantum computers are advancing rapidly, and when they reach full power, they could break much of the encryption in standard use today. That means your sensitive files, from intellectual property and government contracts to healthcare data and personnel records, may not be safe if stored with outdated methods. Alexandria businesses, especially those serving the DIB or government agencies, need to adopt quantum-secure data storage solutions that provide future-proof protection

Gold Comet
Sep 24, 20252 min read


Resilience in Healthcare: What is Cyber Resilience and Why is it Necessary?
This post defines and discusses the need for cyber resilience in healthcare and the best practices to fortify organizational defenses.

Gold Comet
Feb 28, 20243 min read
bottom of page
